Prevention
Why Vulnerability Management?
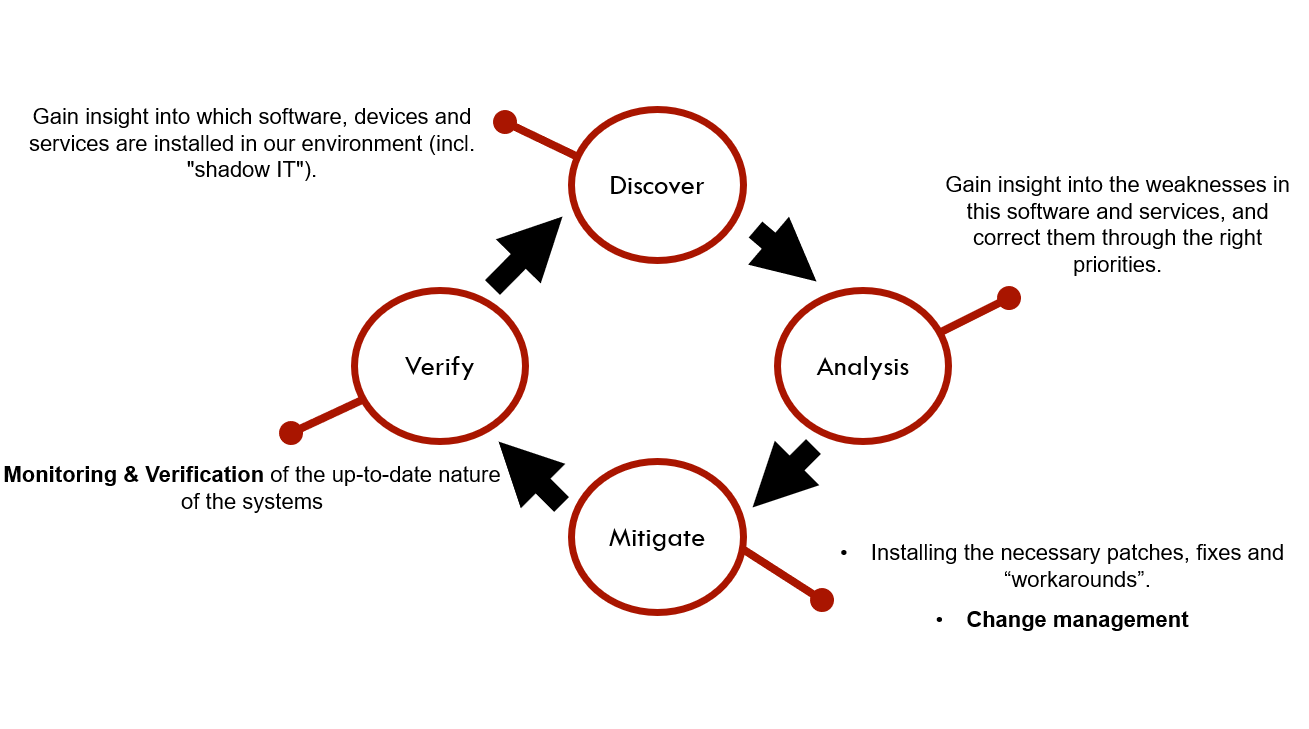
- Reducing security risks in our IT environment
- Gain insight into which software, devices, and services are installed in our environment (incl. “shadow IT”).
- Gain insight into the weaknesses in this software and services, and correct them through the right priorities.
- Follow-up of the up-to-date nature of the systems.
Target
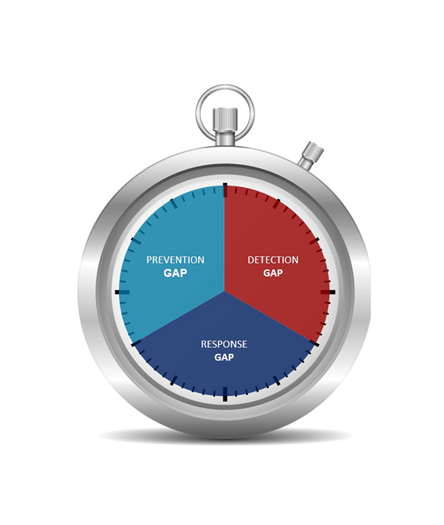
- Timely detection of weaknesses in the environment.
- Avoid that these weaknesses can be exploited by malware/hackers (prevention).
- Serves as input for SOC & Security Incident Management to correctly assess risk and impact (Response).